Expert Tech Insights: Unleashing the Power of Windows, Microsoft 365, and Microsoft Azure
-
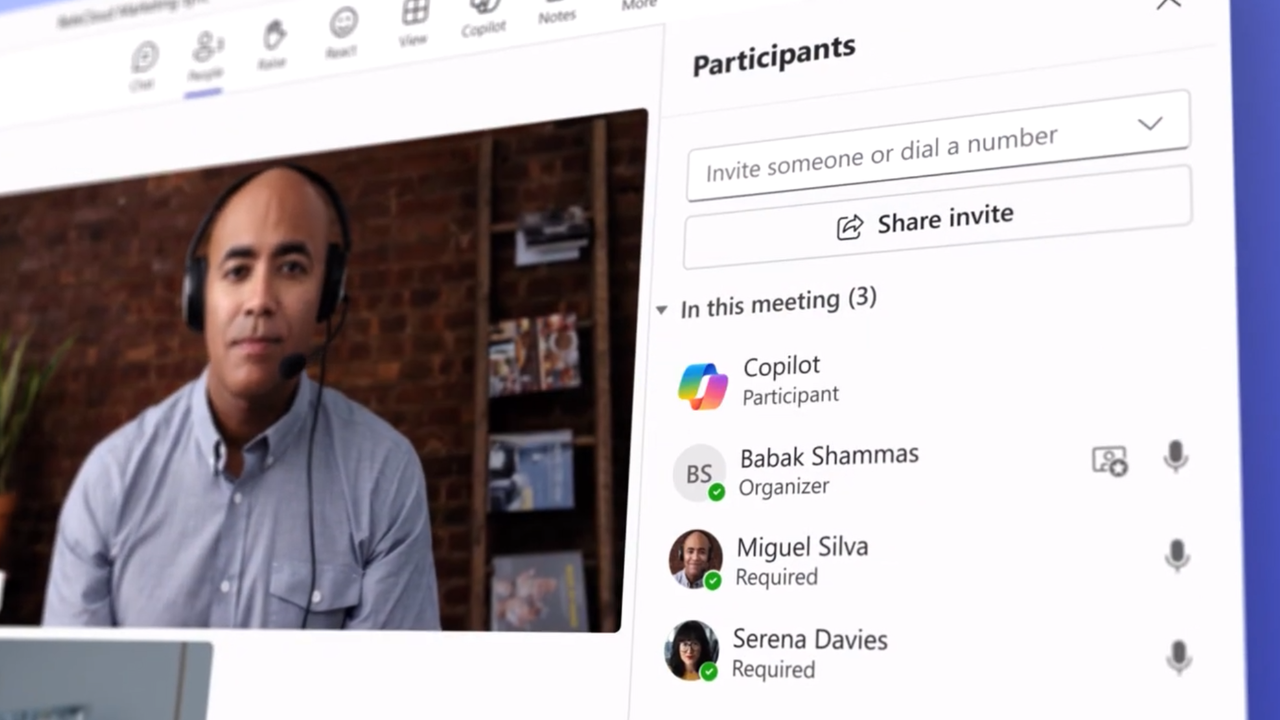
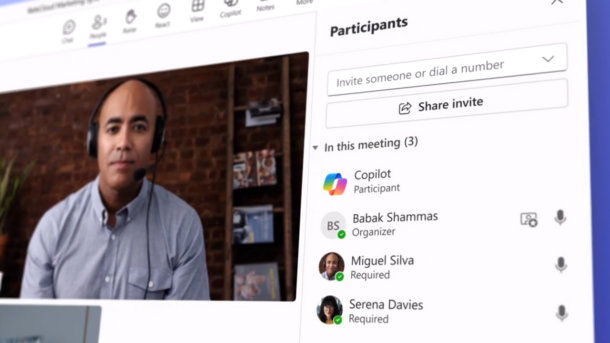
Unlock Productivity: Team Copilot New Features for Microsoft 365
PodcastLast Update: Jun 03, 2024
- May 31, 2024
-
-
Five Tactics Towards Achieving Zero Trust with Microsoft Entra ID (Azure Active Directory)
Last Update: Jun 03, 2024
- Aug 29, 2023
-
-
How Does RAID Data Recovery Work? What to Expect?
This article will provide an overview of the most common RAID levels and the process of RAID data recovery in the event of a failure. RAID, or Redundant Array of Independent Disks, is a virtual storage technology that combines two or more hard drives in a single enclosure to act as one logical unit. There…
Jun 10, 2024Bharat Bhushan
-
Getting Started with DISM PowerShell Cmdlets
Jeff Hicks shows us tips for getting started with the DISM cmdlets in Windows PowerShell, along with steps for adjusting desktop settings with them.
Last Update: Jun 06, 2024
Jun 3, 2015 -
How To Use The DISM Command to Repair Windows 10: A Step-By-Step Guide
In this Ask the Admin, I'll show you how to fix corrupt system files when System File Checker isn't up to the job.
Last Update: Jun 06, 2024
Jul 5, 2018
-
A Guide To Microsoft Office 2024 (LTSC): What You Need To Know
Learn about the new version of Microsoft Office 2024 on the Long Term Service Channel (LTSC). We’ll dive into new features, pricing, expected availability, and the main reasons you should choose this perpetual version vs the hyped Microsoft 365 subscription model. Stay up to date and make informed decisions with this guide. What is Office…
Jun 3, 2024
-
Join Windows 10 to Microsoft Entra ID (Azure AD) During OOBE
Before you perform an AAD domain join, you should understand the difference between an AAD domain-joined device and one that is registered with AAD.
Last Update: Jun 03, 2024
Nov 20, 2019 -
Five Tactics Towards Achieving Zero Trust with Microsoft Entra ID (Azure Active Directory)
For any modern enterprise that uses Microsoft Entra ID (previously Azure Active Directory) to manage user and service access to cloud resources, it’s hard to escape the term Zero Trust (ZT), which implies that your organization must have a layered approach to security. In this article, you’ll learn about five Microsoft Zero Trust tactics for…
Last Update: Jun 03, 2024
Aug 29, 2023
Thank you to our petri.com site sponsors
Our sponsor help us keep our knowledge base free.
Most Popular on Petri
-
Active Directory
How To Install Active Directory Users And Computers: A Step-by-Step Guide
Active Directory is an essential part of Windows Server. It allows IT pros to manage computer resources on the network. In this guide, we’ll show you how to install Active Directory Users and Computers and the basics of working with it so you can manage Active Directory. Active Directory Users and Computers (ADUC) is built…
Last Update: Jun 15, 2023
Aug 12, 2022
-
Windows Client OS
Using Windows Boot Manager to Fix Startup Errors on Windows
Windows PCs may sometimes encounter issues during startup, and that can happen when Windows fails to load properly. In this post, we’ll explain how you can use Windows Boot Manager to troubleshoot boot errors and get your PC up and running again. What is Windows Boot Manager? Windows Boot Manager (Bootmgr.exe) is Microsoft’s proprietary Unified Extensible Firmware…
Last Update: Mar 13, 2024
Jun 29, 2022
-
PowerShell
How to Use PowerShell For Loop, While Loop, and Other Loops
In this article, we will review PowerShell For loops, While loops, Do-While loops, and Do-Until loops. I’ll explain how PowerShell loops are constructed and how to define conditions to enter or exit a loop. PowerShell For loop The For loop is а counting loop, and it’s mostly used when you need to repeat a task…
Last Update: Mar 13, 2024
May 23, 2022
Petri Experts Spotlight
-
-
Russell Smith Editorial Director
-
Laurent Giret Petri Contributor

- First Ring Daily: AI Bedfellows May 31, 2024
- First Ring Daily: The Best Thing Announced May 24, 2024
-
Michael Reinders Petri Contributor

-
-
Stephen Rose Chief Technology Strategist
- UnplugIT Episode 2 – In The Loop Jun 13, 2023
- Unplugging What’s Next for Teams 2.0 May 30, 2023
-
Michael Otey Petri Contributor
- Install and Use SQL Server Report Builder Apr 10, 2024
- SQL Server Essentials: What Is a Relational Database? Mar 12, 2024
-
Chester Avey Petri Contributor
-
Sukesh Mudrakola Petri Contributor

-
-
-
Shane Young Petri Contributor
-
Flo Fox Petri Contributor
-
Sander Berkouwer Petri Contributor
-
-
-
Sagar Petri Contributor
- How to Create a Dockerfile Step by Step Nov 14, 2023
- What is Amazon Kinesis Data Firehose? Jul 14, 2023
-
Bharat Bhushan Petri Contributor
-
Bill Kindle Petri Contributor
-
Sponsored Articles List
-
How to Resolve Exchange Dirty Shutdown Error? A Comprehensive Guide
In this guide, Bharat Bhushan shows you how to diagnose and resolve an Exchange dirty shutdown error and help you to bring the Exchange database back to a clean shutdown state. Thanks to Stellar Info for sponsoring this post. The Exchange Server logs serve as the backbone of data integrity and disaster recovery in Exchange…
Last Update: May 29, 2024
May 28, 2024Bharat Bhushan
-
Active Directory
How to Minimize Your Active Directory Attack Surface
When newly installed, Active Directory’s (AD) default configuration is designed to be easy to use. As a result, attackers can exploit AD to take over your entire network with relative ease. Here’s what you can do to further protect your organization by reducing your Active Directory attack surface. This article is sponsored by Semperis. Securing…
Last Update: May 23, 2024
Feb 1, 2024
-
Active Directory
Learn How Organizations Are Using Semperis Purple Knight to Secure Active Directory
Purple Knight is a free security assessment tool for Microsoft Active Directory that scans the AD environment for indicators of exposure (IOEs) and indicators of compromise (IOCs), provides an overall security score, and offers remediation guidance from identity security experts. This article is sponsored by Semperis. Recently, Petri interviewed several organizations in North America to…
Last Update: May 23, 2024
Jun 7, 2022 -
Cloud Computing
Security
The Ultimate Guide to Web Application Firewalls (WAF)
An often-overlooked element of security is the Web Application Firewall (WAF), especially in cloud computing. In this article, I explain what a WAF does, the different kinds of WAF, and I discuss why you should deploy one or more WAFs in your architecture. What is a Web Application Firewall (WAF)? A Web Application Firewall, often…
Last Update: May 10, 2024
Jun 20, 2023 -
Active Directory
The Role of Identity Threat and Detection Response in Zero Trust Security
I recently spoke to Sean Deuby, who is Principal Technologist at Semperis and an Identity expert. Sean told me about the importance of protecting identities in the current landscape and how Identity Threat Detection and Response (ITDR) is a critical component of the Zero Trust security model. The emergence of cloud computing and the shift…
Last Update: May 10, 2024
Jun 16, 2023
PODCASTS
View all Podcasts-
podcast
Unlocking New Possibilities: Microsoft’s VCF License Mobility Unveiled!
This Week in IT, Microsoft announces license portability for VCF customers, stepping up to an agreement announced between Broadcom and GCP earlier this year. I look at what the new deal involves and how it might help VMware customers. Links and resources In this week’s episode:
Listen now LISTEN & SUBSCRIBE ON: -
podcast
Unlock Productivity: Team Copilot New Features for Microsoft 365
This Week in IT, imagine having a personal assistant for your entire team, automating tasks, managing meetings, and enhancing collaboration effortlessly. Microsoft’s announced a big update to Copilot, which is based on OpenAI’s ChatGPT, that is set to supercharge team productivity. Thank you to Semperis for sponsoring this episode of This Week in IT. Download…
Listen now LISTEN & SUBSCRIBE ON:
OUR SPONSORS
-

ManageEngine
Learn more about ManageEngineMonitor, manage, and secure your IT infrastructure with enterprise-grade solutions built from the ground up.
-
Semperis
Learn more about SemperisReduce time to recover AD after a cyberattack by up to 90%. With Semperis Active Directory Forest Recovery (ADFR), you’ll be back in business in minutes or hours rather than days or weeks.
-

SkyKick
Learn more about SkyKickDid you know data creation is at an all-time high? In fact, it is estimated that 1.7 MB of data is created every second for every person on Earth. As companies grow and adopt more digital tools, the volume of generated data continues to increase, making Data Sprawl one of the key hidden challenges for businesses.